Employee Performance with a Mobile-Optimized Workspace
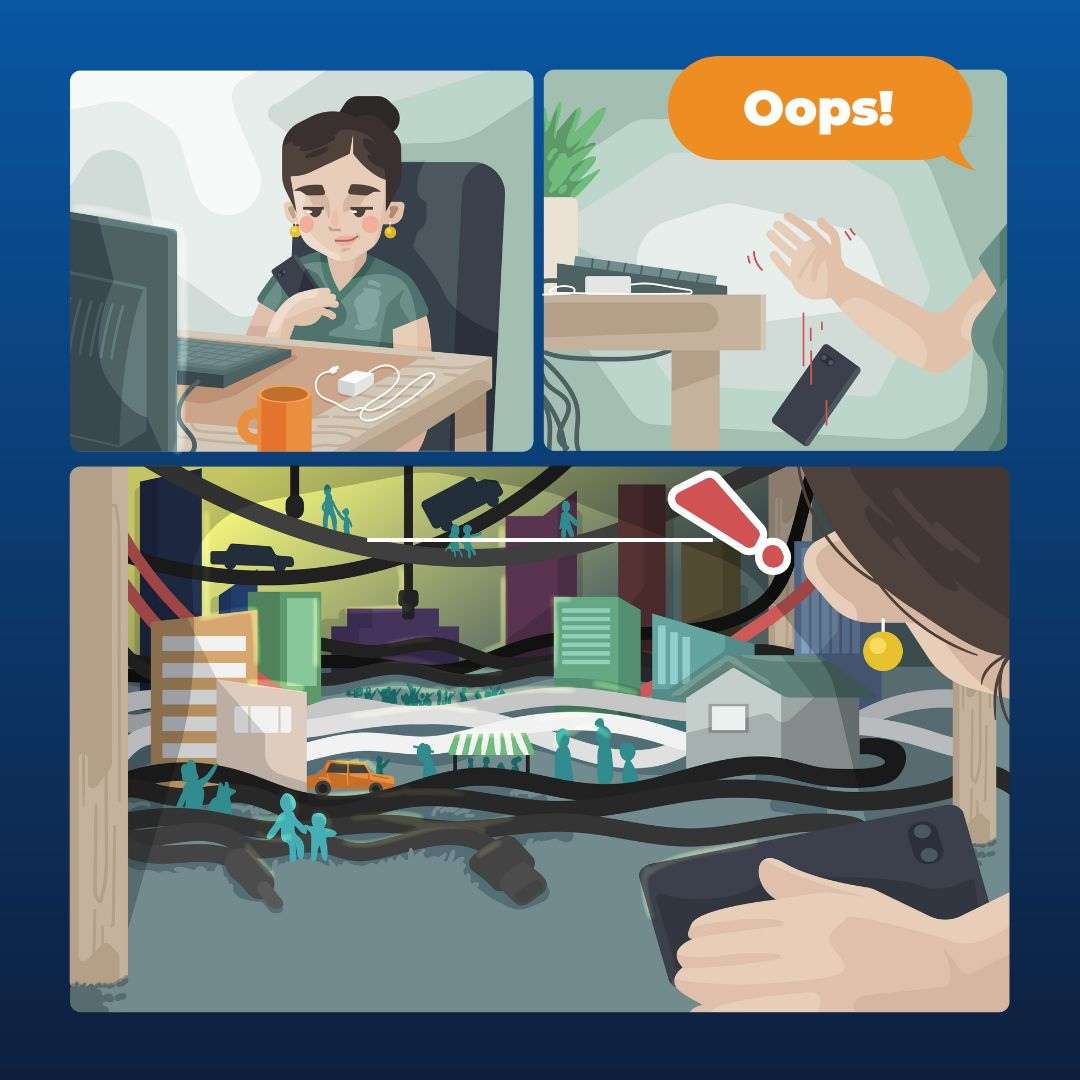
Today’s workspaces transcend physical boundaries. Employees work and collaborate seamlessly from anywhere. Whether they're sipping coffee at a local café or lounging on their living room couch. That's the magic of a mobile- optimized workspace. It’s a game-changer for productivity and performance. 51% of employees use...